* – This article has been archived and is no longer updated by our editorial team –
Below is our recent interview with Adam Perschke, CEO at NOVAM:

Q: Adam, can you tell us more about the company?
A: NOVAM is a distributed cybersecurity company focused on the IoT industry.
NOVAM uses distributed ledger technology and AI to automatically monitor and mitigate IoT threats from the secure boot chain, operating system, mobile application and network. NOVAM also provides auditing & regulatory compliance integration to threat monitoring and detection services to ensure system events are included on an immutable distributed ledger.
NOVAM is the first Artificial Intelligence driven cybersecurity program utilizing DLT to increase the accuracy of its health check. NOVAM not only finds anomalies but also fixes them to boost your tech-immunity system, and even removes threats without prior knowledge of existing danger. Using machine learning and probabilistic mathematics, we plan to offer a security system that is ever-alert, always present and device agnostic.
We provide several solutions to the enterprise:
-IoT monitoring with system health checks and for device visibility
-Autonomous IoT device mitigation from cyber threats
-Tamper-proof auditing and regulatory compliance reporting
Q: What were the founders previous interests or roles prior to starting NOVAM?
A: Adam Perschke, Ian Perschke and Brooks McMillin founded Inteligus Solutions in 2016; an Identity and Access Management (IAM) solutions company. They developed IAM solutions for the leading Hewlett Packard Enterprise OEM in the digital security and surveillance industry, with 50,000+ recording devices spawned across 50 countries, in multi-government embassies, hospitals, correctional facilities, airports, stadiums, universities and retail chains.
Adam Perschke’s experience is in corporate innovation providing guidance on various technologies and future commercial or privatized solutions to the Department of Defense: National Security Technology Accelerator, T-Mobile, Amazon, and Toyota Connected among other organizations.
Ian Perschke specializes in digital surveillance and ran the digital surveillance system for the city of Chicago, including architecture and oversight of the Chicago Police Department system and other B2G entities. He was a liaison for national law enforcement agencies, including the FBI and Homeland Security, for special events.
Brooks McMillin is a cybersecurity specialist having developed and secured custom software within the U.S. Naval Research Laboratory and has worked with internal security and penetration testing with the U.S. Department of Health and Human Services.
 Recommended: Anti-Money Laundering Platform Hummingbird Raises $3 Million In A Funding Round Led By Homebrew
Recommended: Anti-Money Laundering Platform Hummingbird Raises $3 Million In A Funding Round Led By Homebrew
Q: How is your platform supposed to fight cybercrime?
A: NOVAM uses a layered approach to help secure IoT devices and ecosystems to defend against cyber attacks.
We employ a bottom-up approach to security, securing the building blocks of a system. We use distributed ledger technology and IoT system health checks to protect against firmware changes from the bootloader, operating system and application layer by automatically mitigating malware-installs with a fresh up-to-date approved version. Using DLT allows us to provide a tamper-proof auditing and compliance reporting tool for enterprise.
Q: You’ve recently announced partnership with Vault Wallet ; could you tell us something more?
A: We recently announced a partnership with Vault Wallet that enables hardware-level protection of digital tokens on IoT devices and allows them to extend their services by offering real-time IoT security monitoring and mitigation services to their clients. One of our goals at NOVAM is to have service integrations within IoT customers hardware and partnering with Vault Wallet amplifies our service provider mentality.
Q: How did the NOVAM cybersecurity concept spawn?
A: In 2016, the Mirai botnet attacked hundreds of thousands of IoT devices worldwide using default login credentials. The largest automated cyber attack on IoT devices at that time. Using default credentials an IoT device can be authenticated and authorized to do any action, like installing malware, without an alert, automatically compromising it.
NOVAMs research started in 2016 after the Mirai botnet. Coming from the IAM industry we understood that identity management is the first line of defense and if compromised, a device can be infected easily. We determined that not enough standardization would take place quick enough in the IoT industry, which is rapidly developing in terms of devices and usability, but not in security standards.
So, we developed a bottom-up approach starting in the kernel level of a device to ensure a devices firmware and software are authentic and accurate using DLT. We ensure tamper-proof assurity that devices are healthy and uncompromised. If a device is compromised, it’s autonomously mitigated with the most up to date version on multiple levels of the system.
 Recommended: Divvy Homes Has Recently Raised $30M To Accelerate Growth And Expand Market Reach
Recommended: Divvy Homes Has Recently Raised $30M To Accelerate Growth And Expand Market Reach
Q: Tell us more about your token and its role in the system.
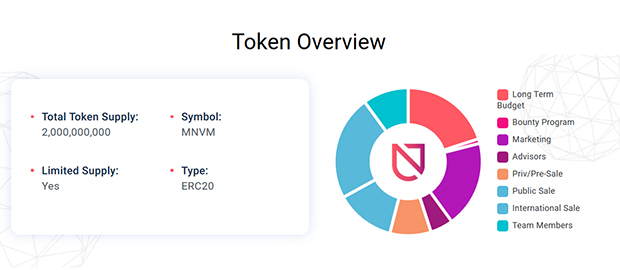
A: The NOVAM Token (MNVM) is a utility token used as a software license to access the NOVAM Network for cybersecurity solutions. The token can be used for system health checks on individual IoT devices or ecosystems of similar devices. Our solutions include monitoring, mitigation, and auditing and compliance reporting tools for IoT devices and ecosystems.
Q: What is on the roadmap for NOVAM moving forward?
A: Our roadmap is expansive and we are excited for the future. We’ll be building out the enterprise-ready solutions for monitoring and autonomous mitigation within an IoT device while working directly with enterprise. We will start to develop our forensic investigation and auditing platform to allow seamless integration into existing enterprise technology stacks and develop the underlying DLT protocols for use within IoT devices, ecosystems and enterprise networks.

